Blog
Multi-Tenant Observability with vCluster: Centralized Metrics and Logs Using Prometheus, Loki, and Grafana
Discover how platform teams can implement centralized metrics and logging for multi-tenant Kubernetes using vCluster. This article walks through such an architecture for private-node vClusters, showing how a centralized observability stack can serve many isolated tenant clusters, laying the foundation for scalable, production-ready multi-tenant observability.
Stop Burning Your LLM Budget: Cost-Efficient LLMOps on Kubernetes
As LLM initiatives mature from pilot to production, infrastructure costs frequently scale faster than the value they deliver. The culprit is often operational inefficiency: idle GPUs, uncontrolled storage growth, cold start latency, and unplanned network egress. We examine the principal cost drivers in LLMOps on Kubernetes and provide actionable best practices across observability, GPU efficiency, throughput tuning, storage governance, and network topology.
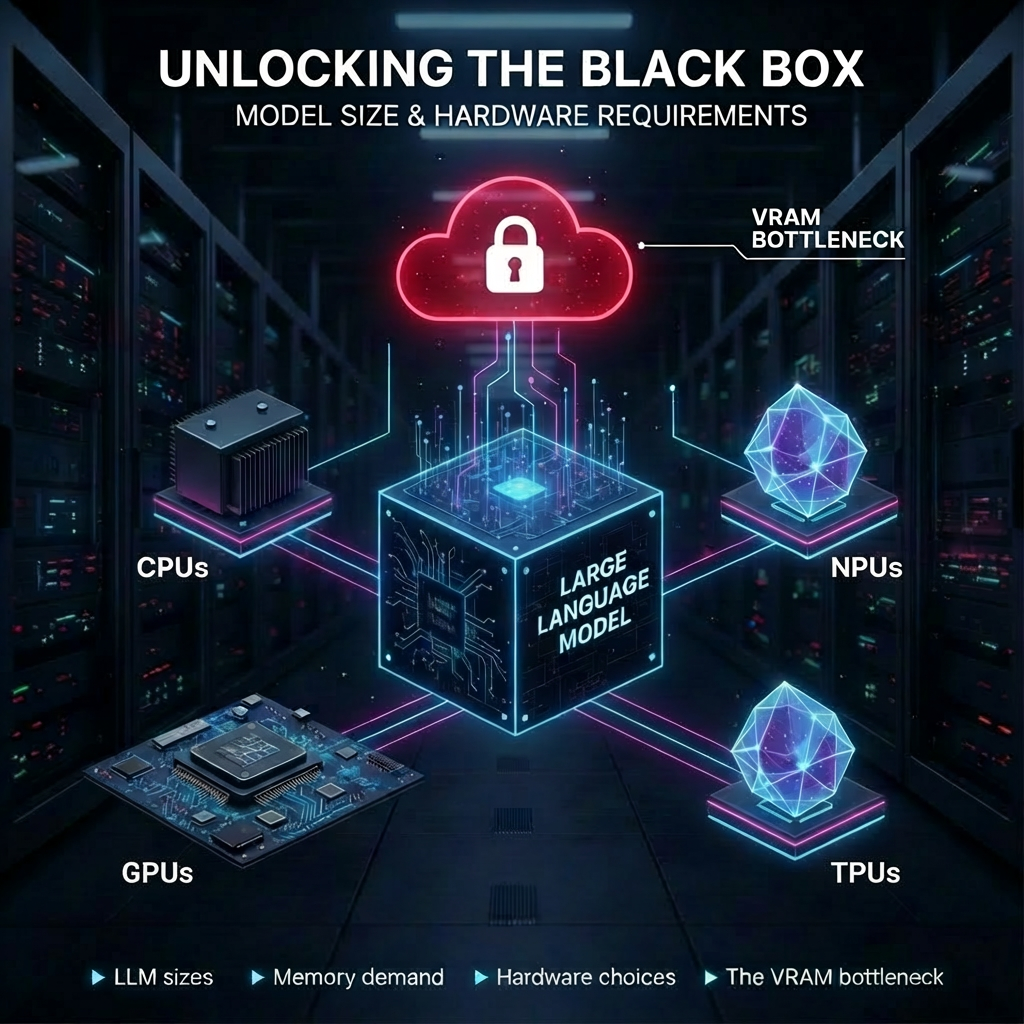
Beyond the Model: The Hardware Decisions That Define Your AI Strategy
Unlocking the black box: How does model size translate into real hardware requirements?
In this post we break down the fundamentals every tech professional should know:
► LLM sizes: overview of LLMs and their intended use ► Memory demand: how to estimate it quickly and reliably ► Hardware choices: CPUs vs GPUs vs TPUs ► The VRAM bottleneck: why memory is the central constraint for inference performance
This is your guide to the engine room of Generative AI.
Dagger: CI/CD as Code and Agentic AI enabler
CI/CD pipelines are supposed to help developers ship better code, and faster. In practice, they quite often do the opposite. Developers still need to write scripts to build and test applications locally. Environment configurations bloat pipelines with opaque and hard-to-reuse YAML code. And as workflows expand beyond CI/CD to integrate agentic AI, traditional tools start to show their limits. Dagger was created to address exactly these problems.
One Prometheus to Rule Them All: Multi-Tenancy Kubernetes with Centralized Monitoring and vCluster Private Nodes
Discover how platform teams can implement centralized metrics for multi-tenant Kubernetes using vCluster. This article walks through observability patterns for both regular vClusters and private-node vClusters, showing how a centralized Prometheus and Grafana stack can serve many isolated tenant clusters, laying the foundation for scalable, production-ready multi-tenant observability.

Isolated GPU Nodes on Demand: Implementing vCluster Auto Nodes for AI Training on GKE